After Apple and Microsoft have (finally!) publicly announced they are ready to pull the plug on Adobe Flash, the first makers of Flash webapps are starting to ditch it in favor of HTML5: As Techcrunch writes, Scribd, an online document hosting service, will focus its efforts on HTML5 from now on.
Scribd co-founder and chief technology officer Jared Friedman tells [Techcrunch]: “We are scrapping three years of Flash development and betting the company on HTML5 because we believe HTML5 is a dramatically better reading experience than Flash. Now any document can become a Web page.”
I am very pleased to hear that. Now that web standards are finally offering the kind of versatility modern web applications need, it is a fantastic development that companies are getting rid of the monster that is Flash. That's good for the user for so many reasons, and it's a great example of what HTML5 can really do.
Update: Ryan points out in the comments that Scribd has a demo document online of what this is going to look like. It's fantastic!
By the way: Another company I would like to see getting rid of Flash (in fact, I never understood why they used it in the first place) is slideshare. They are turning into a de-facto standard for posting presentation slides online, but as of yet, their main UI is solidly in Flash's claws. :(

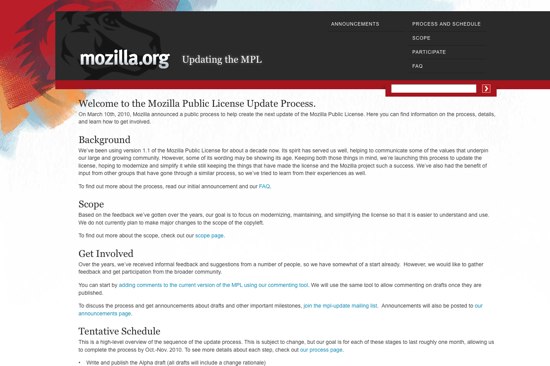
 On a growing number of projects at Mozilla, we use a tool called
On a growing number of projects at Mozilla, we use a tool called